Darknet Markets 2026:
The dark web is part of the deep web but is built on darknets: overlay networks that sit on the internet but which can't be accessed without special tools or software like Tor. Tor is an anonymizing software tool that stands for The Onion Router — you can use the Tor network via Tor Browser.
| Darknet Market | Established | Total Listings | Link |
|---|---|---|---|
| Nexus Market | 2024 | 600+ | Onion Link |
| Abacus Market | 2022 | 100+ | Onion Link |
| Ares | 2026 | 100+ | Onion Link |
| Cocorico | 2023 | 110+ | Onion Link |
| BlackSprut | 2023 | 300+ | Onion Link |
| Mega | 2016 | 400+ | Onion Link |
Updated 2026-04-22
How to Easily Find and Use a Good Darknet Link for Shopping
Locating a functional darknet market link is the first step in a secure procurement process. These links act as direct gateways to platforms where commerce occurs. Users typically find these URLs through specialized forums and link aggregators, which are more reliable than random searches. A stable link is a prerequisite for accessing the market's full ecosystem, which is designed for user convenience and security.
The architecture of a modern darknet market facilitates a straightforward shopping experience. Product listings are organized into clear categories, each with detailed descriptions and often photographs from the vendor. This clarity allows for informed decision-making. The vendor rating system is a critical component, providing a transparent metric of reliability based on past transaction success and communication. High-rated vendors with consistent positive feedback significantly reduce buyer risk.
The procurement process itself is streamlined. After selecting a product, the buyer and vendor communicate through an encrypted internal messaging system. Payment is executed using cryptocurrency, primarily Bitcoin or Monero, which provides a layer of financial anonymity. The transaction is held in escrow by the market administrators until the buyer confirms receipt, protecting both parties. Following payment, the vendor arranges for discreet and reliable logistics. Packaging is designed to be nondescript to ensure privacy during delivery, which is a standard expectation for consumer satisfaction. Maintaining operational security throughout, using tools like the Tor browser and VPNs, is fundamental for safe and sustained access to these services.
Direct Links Make Darknet Shopping Simple
Darknet market links function as direct cryptographic gateways to specialized e-commerce platforms. These links, typically a string of random characters ending in .onion, are accessed through the Tor browser, which anonymizes connection traffic. The link itself is a precise address, similar to a street address in the clear web, but it points to a server hidden within the Tor network's layers of encryption.
Each market link provides a secure portal where the entire procurement process is consolidated. Upon entry, users encounter a familiar interface: product listings, shopping carts, and vendor profiles. The architecture is designed for efficiency, minimizing the steps between product discovery and purchase. This direct access model eliminates intermediaries, fostering a peer-to-peer environment where vendors and consumers interact with reduced external interference.
The reliability of a link is paramount. A stable, frequently updated link indicates robust market infrastructure, leading to consistent uptime and transaction processing. Users verify links through trusted community resources to avoid phishing sites, as a legitimate gateway ensures all subsequent security measuresfrom vendor communication to financial exchangeare built upon a authentic foundation. The link is the first critical component in a chain of operational security protocols.
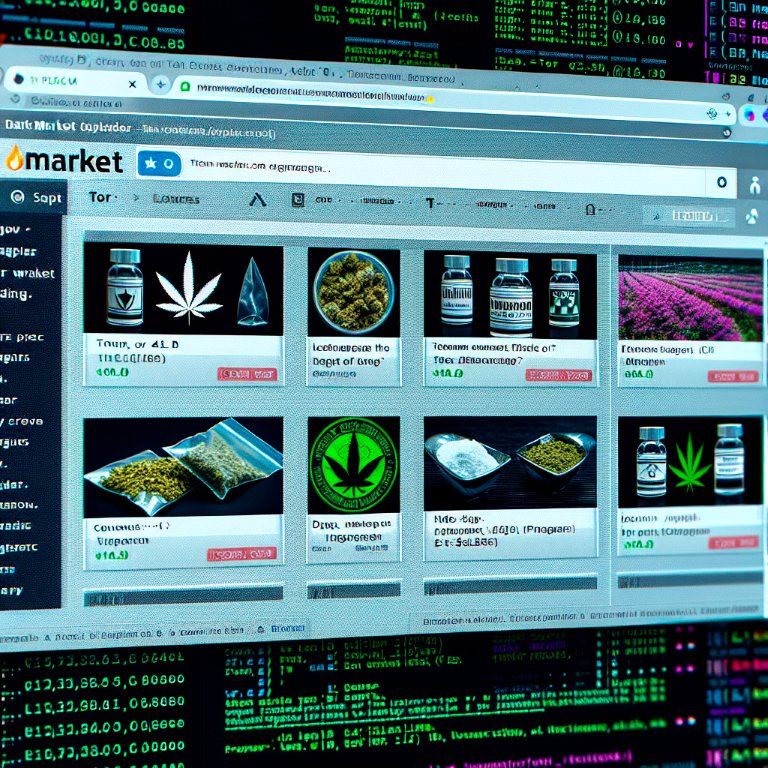
Wide Selection and Clear Info on the Darknet
The product variety on a darknet market is its primary asset. These platforms function as comprehensive digital dispensaries, offering a range of substances that surpasses what is typically available in localized physical markets. A user can find everything from common cannabis strains and MDMA to prescription medications and specialized research chemicals. This extensive catalog is systematically organized into categories and subcategories, enabling efficient navigation and product discovery based on specific chemical properties or desired effects.
Detailed product descriptions are fundamental to the procurement process. Vendors provide precise specifications to establish trust and reduce ambiguity. A standard listing includes:
- The exact substance name and its common aliases.
- Purity percentage or concentration, often verified by the vendor's own testing.
- Clear photographs from multiple angles, sometimes with scale for size reference.
- Explicit dosage guidelines and expected onset/duration of effects.
- Country of origin or synthesis, and the shipping location.
This level of detail allows for informed decision-making. A buyer can compare different offers not just on price, but on the quantifiable quality and characteristics of the product. Descriptions often note the substance's appearance, smell, and texture, which are critical for verification upon receipt. The transparency in these listings creates a consumer-oriented environment where product knowledge is prioritized, leading to more satisfactory transactions and higher vendor ratings. The catalog's breadth and depth, combined with rigorous descriptions, effectively replicate and often exceed the informational standards of legal e-commerce platforms.
How Vendor Ratings Make Buying on the Darknet Safer
The vendor rating system is a core mechanism for establishing trust and ensuring quality on darknet markets. It functions as a direct feedback loop from the consumer community, providing a quantitative and qualitative measure of a seller's reliability. A high rating is not merely a badge of honor; it is a critical indicator of consistent performance across several key operational parameters.
These systems typically break down into several components. The overall rating percentage offers a quick glance at vendor reputation, often calculated from hundreds of past transactions. More insightful are the detailed feedback comments, where buyers describe their experience with product quality, shipping speed, and stealth packaging. Markets also feature separate metrics for communication, shipping time, and item description accuracy. A vendor with a 4.95/5 score over 2000 sales has demonstrated a predictable and satisfactory service pattern.
The analysis of these ratings reduces uncertainty for the buyer. It allows for informed decision-making based on peer verification rather than vendor promises alone. Positive trends in feedback signal a vendor's commitment to maintaining their standing, as their business depends directly on this public record. Common elements found in high-rated vendor profiles include:
- Detailed product listings with verified photographs
- Consistent shipping times and professional stealth methods
- Responsive and professional dispute resolution
- Transparent policies on shipping and refunds
Engaging with this system requires active participation from buyers. Leaving accurate feedback after a completed transaction reinforces the ecosystem's integrity. It creates a self-policing environment where reputable vendors are rewarded with more business, and substandard operators are quickly identified by declining scores. This collective verification process is what enables efficient and secure procurement, making the rating system the most practical tool for assessing vendor legitimacy.
How Darknet Markets Make Buying Easy and Secure
The procurement process on a darknet market is engineered for efficiency and user autonomy. It begins with selecting a product from a vendor with a strong reputation score and positive feedback. The buyer adds the item to a digital cart, similar to mainstream e-commerce platforms.
Proceeding to checkout involves selecting a shipping option. Vendors offer various methods, with discreet packaging being a standard, non-negotiable feature. The buyer then sends the exact cryptocurrency amount, typically Bitcoin or Monero, to a generated escrow address. This system holds the funds securely until order completion.
The transaction timeline is clear:
- Funds are confirmed in escrow.
- The vendor is notified and dispatches the order.
- The buyer receives tracking information, if offered.
- Upon successful delivery, the buyer finalizes the order, releasing escrow funds to the vendor.
This escrow mechanism is fundamental, protecting the buyer by ensuring payment is only released after confirmation of delivery. It creates a self-regulating environment where vendor reliability is directly tied to financial reward. The entire process minimizes unnecessary interaction, reduces human error, and standardizes a secure exchange of goods.

How Crypto and Escrow Make Darknet Purchases Safe and Easy
The financial architecture of darknet markets is built upon cryptocurrency, primarily Monero (XMR) and Bitcoin (BTC). This system provides a necessary layer of financial privacy that traditional payment methods cannot offer. Transactions are recorded on a public ledger, or blockchain, but they are pseudonymous, meaning they are linked to a digital wallet address rather than a person's real identity.
To enhance security, markets employ an escrow service. When a buyer places an order, their cryptocurrency is held in escrow by the market's automated system. The funds are only released to the vendor after the buyer confirms satisfactory receipt of the product. This mechanism protects buyers from fraudulent vendors who might not ship items and protects vendors from fraudulent chargebacks. For additional security, many experienced users engage in multisignature (multisig) escrow, which requires two out of three cryptographic keys to release funds, further reducing reliance on the market's central authority.
The process is streamlined:
1. A user acquires cryptocurrency from an exchange.
2. Funds are transferred to a private, non-custodial wallet like Electrum or Cake Wallet.
3. From this personal wallet, the exact amount is sent to the unique deposit address generated by the darknet market.
4. Once the deposit is confirmed, the user can finalize a purchase, with the funds held in escrow until completion.
This financial model creates a trustless environment where commerce can proceed based on cryptographic proof and decentralized consensus rather than personal trust. The use of cryptocurrency, combined with escrow, establishes a secure and efficient economic framework that supports the entire procurement process, from product selection to finalizing a sale.
Secure Steps for Safe Dknet Shopping
Operational security, or opsec, is the foundational practice for safe drknet access. It begins with using the Tor Browser, which anonymizes your connection by routing it through multiple encrypted nodes. This prevents your internet service provider from seeing your final destination. For enhanced privacy, connecting via a VPN before launching Tor adds an extra layer of encryption to your initial connection, masking Tor usage itself.
Accessing market links requires meticulous verification. Verified mirrors and dark.fail are essential resources for finding legitimate URLs, as phishing sites are a primary threat. These fake sites mimic real markets to steal login credentials and cryptocurrency. Always verify a link through multiple independent sources before proceeding.
Once on a market, maintaining anonymity is critical. This involves:
- Creating a unique username never used elsewhere.
- Using a strong, randomly generated password managed by a password keeper.
- Enabling two-factor authentication (2FA) to protect your account from takeover.
Secure communication with vendors is conducted via the market's built-in PGP encryption. You use the vendor's public key to encrypt your address, which only their private key can decrypt. This ensures sensitive information is never exposed on the market servers, even in the unlikely event of a data breach. Never send your address in plain text.
Finalizing an order involves releasing escrow funds only after the product arrives and meets the description. This escrow system protects the consumer by holding payment until satisfaction is confirmed, incentivizing vendors to provide quality products and reliable logistics. Discreet packaging and professional logistics are standard, ensuring seamless delivery and consumer satisfaction.

How Customer Reviews Build Trust on the Darknet
Consumer satisfaction is the primary mechanism for maintaining quality and trust within darknet markets. The system is built on transparent feedback, where every transaction concludes with a public review and rating. This creates a self-regulating environment where vendors with consistently high ratings and positive reviews are prominently featured, while those with poor performance are marginalized. The review process is comprehensive, covering product quality, shipping speed, packaging discretion, and communication. This detailed feedback loop provides future buyers with reliable, peer-verified data for making informed decisions.
The emphasis on satisfaction directly influences market dynamics. Vendors invest significant effort into customer service and product consistency to maintain their high standing. Common practices include:
- Reshipping policies for orders that are lost or seized.
- Responsive and professional communication to resolve any issues.
- Accurate product listings with detailed descriptions and photographs.
Smooth Delivery in the Darknet
The final and most critical phase of the procurement process is the physical delivery. Darknet markets have developed highly sophisticated logistics chains to ensure product arrival. This system relies on professional stealth packaging and established shipping methods to bypass routine inspections.
Vendors invest significant effort in making packages appear ordinary. Contents are vacuum-sealed to prevent odor and then hidden within layers of common items. The external packaging is generic, often using recycled materials to avoid drawing attention. Shipping labels are typed or printed to eliminate handwriting analysis, and return addresses are frequently falsified.
The reliability of a vendor's logistics is directly reflected in their rating and feedback. Consistent positive reviews regarding stealth quality and delivery times indicate a trustworthy operation. Customers prioritize vendors who use multiple postal services and offer tracking options, as this demonstrates a systematic and professional approach. The entire process is designed for plausible deniability, ensuring the package gives no indication of its true contents if intercepted.
Successful delivery completes a cycle built on cryptographic security, vendor accountability, and logistical precision. This end-to-end integration allows for a consistent and secure consumer experience.