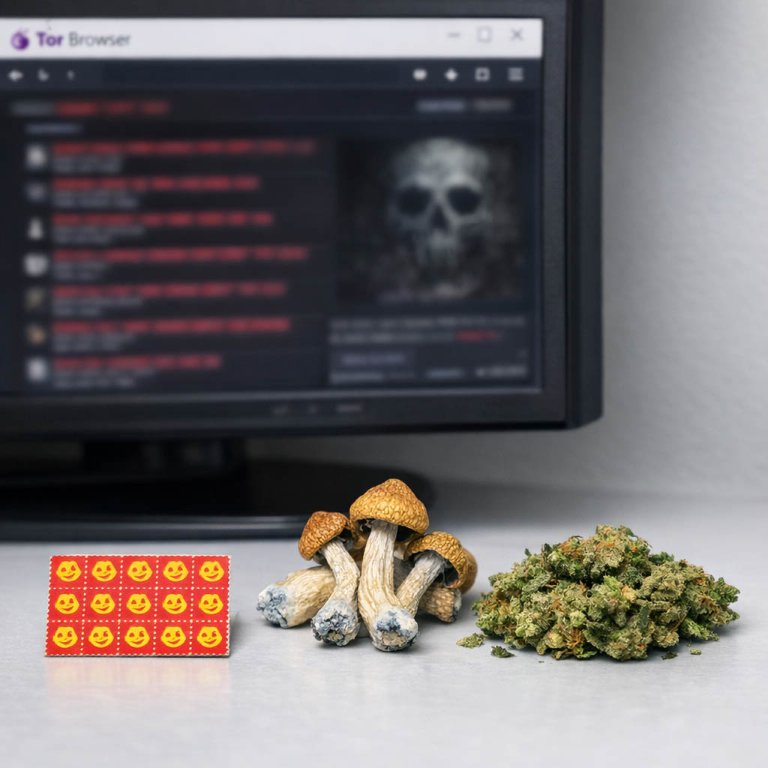
Darknet Markets 2026:
The dark web is part of the deep web but is built on darknets: overlay networks that sit on the internet but which can't be accessed without special tools or software like Tor. Tor is an anonymizing software tool that stands for The Onion Router — you can use the Tor network via Tor Browser.
| Darknet Market | Established | Total Listings | Link |
|---|---|---|---|
| Nexus Market | 2024 | 600+ | Onion Link |
| Abacus Market | 2022 | 100+ | Onion Link |
| Ares | 2026 | 100+ | Onion Link |
| Cocorico | 2023 | 110+ | Onion Link |
| BlackSprut | 2023 | 300+ | Onion Link |
| Mega | 2016 | 400+ | Onion Link |
Updated 2026-04-22
How the darknet builds trust for safe shopping
The darknet functions as a secure marketplace by implementing systems that mirror and often exceed the trust mechanisms of conventional e-commerce. A user's ability to find quality and engage in secure commerce hinges on two interconnected pillars: vendor reputation and product verification.
Every major darknet market incorporates a detailed feedback system. Customers rate their purchases on specific criteria like product accuracy, shipping speed, and stealth packaging. This cumulative data generates a vendor score and is displayed alongside written reviews. High-volume vendors with consistently positive feedback become trusted entities, as their commercial success depends entirely on maintaining this reputation. Disputes are often mediated through escrow services, where cryptocurrency funds are held by the market until the buyer confirms satisfactory receipt of the goods, thus protecting both parties.
Product quality is assessed directly through this crowd-sourced feedback. Reviews frequently contain technical analyses, with buyers conducting and reporting their own purity tests. This creates a transparent environment where product listings with inferior or misrepresented items are quickly identified and negatively rated, driving them from the marketplace. The variety available allows for direct comparison between vendors, fostering a competitive environment that rewards high standards. Accessing these platforms requires specific software, like the Tor browser, which provides the necessary anonymity for such transactions to occur. Operational security knowledge, such as using encrypted communication and avoiding common mistakes, is essential for user protection and is widely discussed in community forums, completing the ecosystem for secure trade.
How Darknets Make Buying Drugs Safe and Reliable
The foundation of secure commerce on darknet platforms is the establishment of trust and quality assurance without traditional identifiers. This is achieved through a multi-layered system where technological features and community-driven feedback converge to create a reliable trading environment.
Vendor reputation systems are the primary mechanism for maintaining market standards. Each seller accumulates a public history of transaction reviews, detailed ratings, and resolution rates for disputes. A vendor with a long-standing positive record and thousands of successful sales provides a quantifiable measure of reliability. Buyers prioritize these established vendors, which incentivizes consistent product quality and professional service to protect one's business standing.
The variety and specification of products available further support informed purchasing decisions. Listings are typically comprehensive, including:
- High-resolution photographs with verification markers
- Precose chemical analyses or purity percentages
- Clear information on quantity and intended effects
This level of detail allows for direct comparison and sets clear expectations, reducing the uncertainty inherent in anonymous trade. The escrow service model secures the financial transaction, holding the buyer's cryptocurrency until the product is received and confirmed as described. This system directly protects the buyer and ensures vendors are paid for fulfilled orders, aligning the interests of both parties toward a successful exchange.
Operational security knowledge, while a protective measure for the user, also contributes to overall market stability. When users properly employ encryption, anonymizing software, and secure communication protocols, it reduces systemic vulnerabilities, leading to fewer market disruptions and more consistent platform availability for commerce.
How Cryptocurrency Makes Buying on the Darknet Easy and Secure
The inherent design of cryptocurrencies like Monero and Bitcoin provides the financial architecture necessary for darknet commerce. These digital currencies enable pseudonymous transactions that are recorded on a public ledger but are not directly tied to real-world identities without additional information. This creates a layer of financial privacy that traditional banking systems cannot offer.
The transaction process is direct. A buyer transfers cryptocurrency from their private wallet to the vendor's address, often utilizing a market's escrow system for security. The decentralized nature of these currencies means no central bank or government can freeze or reverse the payment, ensuring the trade's finality and protecting both parties from financial censorship.
Cryptocurrencies are not just tools for payment but are integral to the trust models on these platforms. The use of multisignature escrow, which requires two out of three cryptographic keys to release funds, minimizes fraud. This technical feature, built on cryptocurrency protocols, allows a third party, the market administrator, to arbitrate disputes without ever holding the funds directly, thus securing successful trade completion.

How Escrow Makes Darnet Drug Trades Safe and Smooth
The escrow system is a fundamental component for secure commerce on darknet markets. It functions as a neutral third-party service that holds the buyer's cryptocurrency payment until the transaction terms are fulfilled. This mechanism directly addresses the inherent trust deficit in anonymous environments. When a purchase is initiated, funds are locked in the market's escrow wallet. The vendor is notified and proceeds with shipping the product. Only after the buyer receives the order and confirms its satisfactory condition are the funds released to the vendor. This process creates a balanced power dynamic, incentivizing both parties to act in good faith.
The practical operation involves a clear sequence. A buyer selects a product and submits payment, which is then held in escrow. The vendor sees the secured payment and dispatches the order. Upon delivery, the buyer finalizes the transaction, triggering the escrow service to transfer the cryptocurrency to the vendor. If a dispute arises, such as non-delivery or substandard quality, the buyer can open a dispute resolution case. Market moderators, often experienced users or administrators, then review communication and evidence from both sides before adjudicating the release of funds. This structured approach significantly reduces the risk of fraud.
For the system to maintain integrity, the escrow service must be administered by the market platform itself or a highly trusted external party. The security of these held funds is paramount; a market exit scam, where administrators abscond with all escrow funds, represents a critical systemic failure. Therefore, the reputation and operational history of a darknet market are closely tied to its reliable management of escrow. Successful trade completion relies on this temporary custodial function, which enables a wide variety of commerce by providing a basic framework of security and accountability where traditional legal contracts are not enforceable.
Great Selection and Quality on the Darknet
The darknet's commercial ecosystem is distinguished by a competitive market that directly incentivizes product quality. Vendors operate on a reputation-based system where customer feedback is public and permanent. This creates a direct economic pressure to provide high-purity substances and accurate product descriptions, as negative reviews severely impact future sales. The anonymity of the platform paradoxically fosters a form of market-driven accountability not always present in unregulated street markets.
Product variety is extensive, catering to specific consumer demands. Available inventories typically include:
- Pharmaceutical-grade compounds with verified chemical structures.
- Botanical substances sourced from specific global regions.
- Prescription medications, often from international suppliers.
- Designer research chemicals with detailed dosage information.
This variety is supported by vendor-provided analytical data, such as gas chromatography-mass spectrometry (GC-MS) test results, which verify compound identity and purity. Forums associated with these markets feature user-led harm reduction discussions, where experiences with specific vendors and batches are shared. The resulting environment allows for informed consumer choice based on empirical evidence rather than hearsay, reducing risks associated with adulterated products.
How Reputation Systems Build Trust on Darknet Markets
The vendor reputation system is the fundamental mechanism ensuring reliability on darknet markets. These systems transform anonymous commerce into a structured environment where trust can be quantified. A typical system aggregates feedback from completed transactions, generating a visible score or rating for each seller.
This score is calculated from several data points provided by buyers:
- The accuracy of the product description versus what was received.
- The speed and discretion of shipping.
- The quality of communication from the vendor.
Beyond simple ratings, advanced systems incorporate escrow protection and dispute resolution. Funds are held in escrow until the buyer confirms satisfactory receipt, which prevents scams. If an issue arises, market moderators can review communication and evidence before releasing funds, a process that incentivizes honest behavior from both parties. This creates a self-regulating ecosystem where reputable vendors flourish, while those with poor feedback or unresolved disputes are marginalized.
The result is a stable commercial platform. Buyers can make informed decisions by comparing vendor histories, reducing the risk of financial loss. For vendors, maintaining a strong reputation becomes a valuable business asset, encouraging high standards in product quality and customer service. This feedback loop is what sustains market integrity and facilitates secure, repeat transactions on darknet sites.
Software for Safe and Private Shopping on the Darknet
Accessing darknet commerce platforms requires specific software that establishes a foundation for security and anonymity. The primary tool is the Tor Browser, which routes internet traffic through a distributed network of relays, obscuring a user's location and usage from network surveillance. This browser provides access to .onion domains, which are the standard addresses for darknet markets.
For transactions, cryptocurrency wallets are essential software components. Bitcoin remains prevalent, but privacy-focused coins like Monero are increasingly standard due to their enhanced obfuscation of transaction details. A dedicated wallet, separate from exchanges, provides greater control over private keys.
Operational security extends beyond basic access. Users often employ:
- Full-disk encryption (e.g., VeraCrypt) to protect data at rest.
- Virtual Private Networks (VPNs) as an optional supplemental layer.
- Secure operating systems like Tails, which runs amnesiac sessions leaving no digital trace on the host hardware.
This software suite creates the necessary environment. It allows buyers to connect to vendor storefronts, review escrow-protected listings, and engage in transactions where cryptocurrency and reputation systems facilitate trust. The technical barrier imposed by this software inherently fosters a more deliberate and informed user base, contributing to the overall stability and reliability of the commercial ecosystem.

Simple Security for Safe Darknet Shopping
Operational security is the foundational practice that enables secure commerce on darknet sites. It begins with the correct use of specialized software, primarily the Tor Browser, which anonymizes network traffic by routing it through multiple encrypted layers. This process conceals a user's actual IP address and physical location, creating the essential condition for anonymous browsing and transaction initiation.
Beyond basic access, effective security requires compartmentalization. This means separating one's darknet activities completely from any personal or clearnet identity. Users employ dedicated pseudonyms and avoid reusing usernames or email addresses associated with their real lives. For financial transactions, cryptocurrencies like Monero or Bitcoin are used with additional privacy measures. This involves using intermediary wallets to break the direct on-chain link between a user's primary exchange account and the final darknet market deposit address, adding a critical layer of financial obfuscation.
Technical configurations are equally vital. A comprehensive security setup includes:
- Enabling the highest security setting within the Tor Browser to disable potentially vulnerable web features.
- Using a reputable VPN service in conjunction with Tor, configured correctly to avoid leaks, for an added network layer.
- Employing a secure operating system such as Tails or Qubes OS, which are designed to leave no digital footprint on the host hardware.
- Practicing meticulous communication hygiene, using PGP encryption for all sensitive messages with vendors and never discussing operational details outside secured channels.
This layered approach to security directly supports the ecosystem's economic functions. By mastering these techniques, users protect themselves and contribute to the overall resilience of the marketplace. Their ability to operate securely allows them to confidently engage with vendor reputation systems and escrow services, which in turn facilitates the reliable exchange of high-quality goods. The knowledge is not peripheral; it is the operational framework that makes the anonymous, trust-based commerce of the darknet possible and sustainable.